2G 3G 4G IMSI Catcher
- 1. What is IMSI Catcher? IMSI catcher is a hi-tech self-detective device that can be widely used for NSA, Public Security, the army, a……
Product Details
1. What is IMSI Catcher?
IMSI catcher is a hi-tech self-detective device that can be widely used for NSA, Public Security, the army, and the other confederacy agency. It is based on the BTS working principles and some relevant small-cell solutions. It is small in size, low consumption, intelligent, and has easy maintenance features.
The Stone IMSI Catcher is a multi-functional catcher which acquires GSM, UMTS, LTE, and NR cellular devices within its coverage area and extracts their cellular identities (IMEI, IMSI, and SUCI). The unit, which can be set up in any scenario, can also detect the presence of all cellular phones in restricted areas where it is deployed and issue an alert if a predefined target device is identified.
It is also equipped with various software configurations to meet many practical needs. It can provide advanced analytics (such as Accompany Analysis, Permanent analysis, Track Analysis, and Crash Analysis ). It is easily integrated into other intelligence-gathering systems and works across all cellular makers, operating systems, and technologies such as GSM/UMTS/LTE 2G/3G/4G/5G (NSA and SA).
It supports 2G/3G/4G/5G full band scanning and collects info at a super rate. The device detects all the surrounding active mobile IMSI in silence mode and it won’t disturb standard mobile communication. The captive ratio can reach 99%.
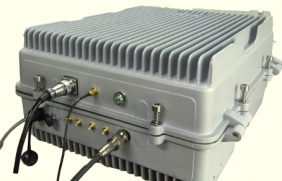
It comes in various form factors and configurations: a highly compact unit that fits into a jacket pocket for close contact covert operations; ruggedized suitcase or backpack portable units; vehicle-mounted for flexible deployments; and fixed, rack-mounted units for long-term operations. Moreover, configurations may be customized to specific customer needs, leveraging that all system components are developed in-house. Furthermore, Stone IMSI Catcher is an all-in-one system that supports GSM, UMTS, LTE and 5G technologies, including all relevant frequency bands in multi-cells configurations.



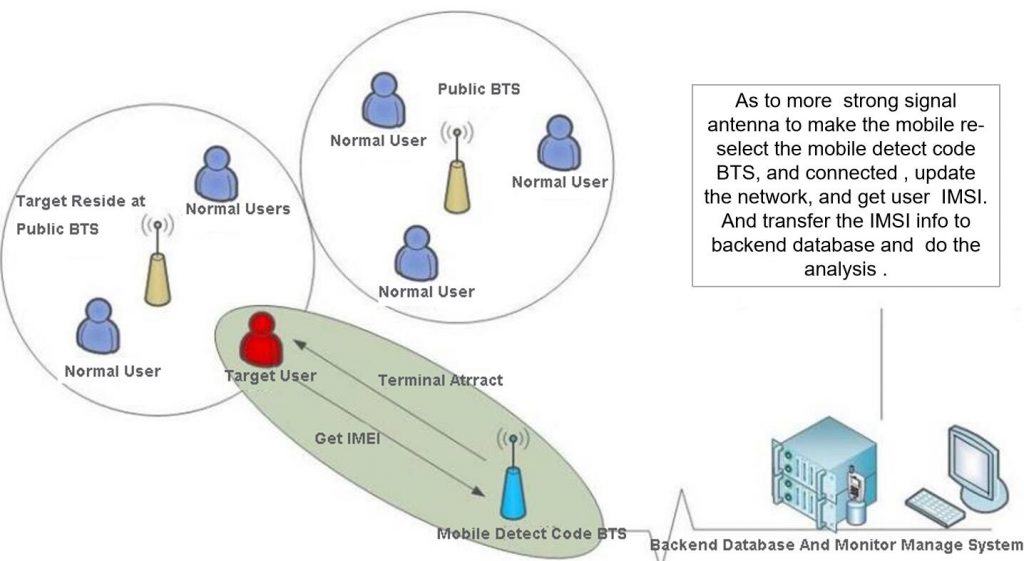
2. IMSI Catcher System Structure
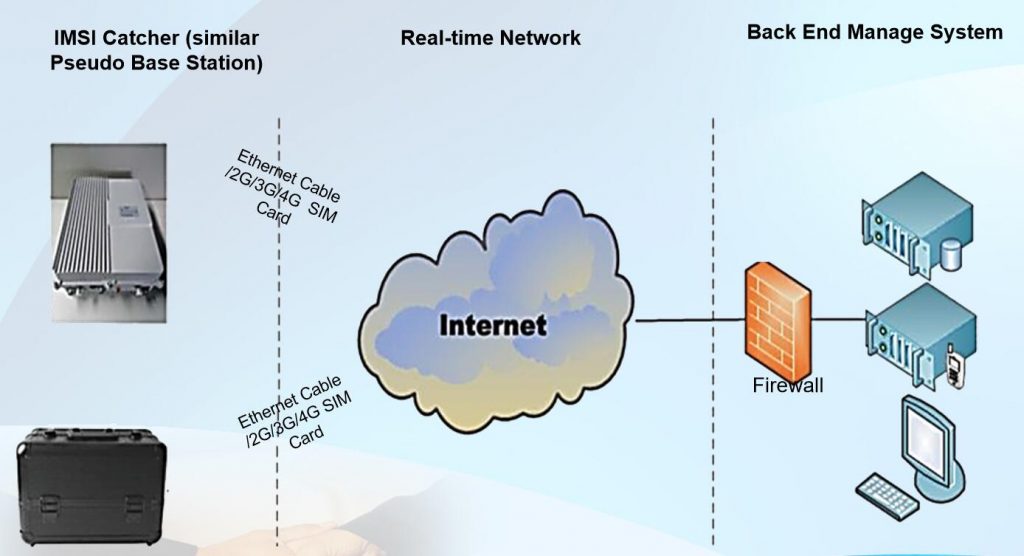
3. IMSI Catcher Working Principle
4. IMSI Catcher Main Features
- High Captive Ratio:In static over 99%;60km/h over 97%;80km/h over 95%Below120km/h over 92%
- Large Captive Quantity: 4G Maximum 3000 set/min; 2G Maximum 2700 set/min.
- Low Power Consumption: GSM<80W、4G Full band working:180W/ In static:45W(shut off amplifier)
- Small Size:4G Full Band <20kg, module<3kg;2G+4G can be in one set
- Low interference: Use 5MHz, TDD sync with Public BTS. 0 interference to Operator
5. IMSI Catcher Parameters
| No. | Type | Details |
| 1 | Protocol | Support GSM、CDMA、WCDMA、TD-LTE、FDD-LTE |
| 2 | Working Method | Active |
| 3 | Radiate Power | Maximum 20W(Adjustable) |
| 4 | Receiving Sensitivity | -100dBm |
| 5 | Scan IMSI speed | >800个/min/carrier |
| 6 | Statics Captive Ratio | >99% |
| 7 | Dynamic Captive Ratio | 40-60km/h:>97%; 60-85km/h: >95% |
| 8 | Coverage Area | 300~800 meters It depends on the device's power, antenna, and the environment |
| 9 | Target Release | Affect Standard Communication:<1 second; Can set not to captive the same device at a certain time. Support Time arrangement |
| 10 | Data recall back method | Wireless or Cable |
| 11 | Install Method | Fix/Car carry/Module Install |
| 12 | Protection Class | Waterproof, dustproof, IP65 |
| 13 | Antenna Lighting Protection | Optional |
| 14 | Weight | Full Sets<20kg, Module <3kg (depends on the power and protocol) |
| 15 | Size | Depends on the power and protocol |